19.3 Local versus remote attacks
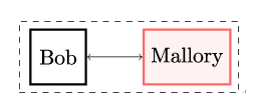
Geographic constraints imposed on the attacker form the second fundamental attack characteristic in practical cryptography and information security.Figure 19.3 shows a local attack where Mallory needs to be co-located with Bob. What the term co-located exactly means depends on the specific attack.
In some cases, the term co-located refers to Mallory residing on the same machine. As an example, imagine an attack where Mallory tries to steal Bob’s password from the password file stored on a machine running a Linux operating system that is not connected to the internet. An example might be a machine in a factory. To perform such an attack, Mallory must be logged in on the same system like Bob and therefore must be able to get into the vicinity of that system.
In other cases, a local attack may require Mallory to be connected to the same local network as Bob. If Bob’s machines on his computer network trust each other by default and allow every access from within the network, Mallory only needs to get access to that network to extract confidential documents.
What both examples have in common is that Mallory’s geographic location is constrained by that of Bob. Of course, a Local Area Network (LAN) could span one or more buildings or even an entire campus. Furthermore, the site where the machine storing the password file is located could be in a huge manufacturing facility. Nevertheless, all these locations – however large they might be – are geographically confined.
In some cases, Mallory needs to physically access Bob’s hardware. As illustrated in Figure 19.4, Mallory gets inside Bob’s machine or device to be able to directly interact with Bob’s hardware.
A prominent example of an attack exploiting physical access is the hacking of embedded devices via JTAG, a standard debug interface on microcontrollers used in such devices. Being designed for debugging and testing, JTAG allows access to and the modification of internal registers and memory, including re-programming and re-configuring the microcontroller. As a result, if Mallory gets access to Bob’s JTAG interface, she can easily compromise Bob’s system without ever breaking a cryptographic mechanism.
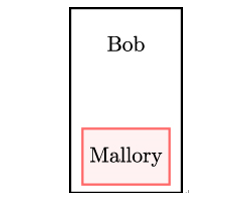
Figure 19.4: Attack requiring physical access
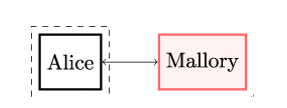
In a remote attack, shown in Figure 19.5, Mallory is able to compromise Bob’s security from a remote geographical location, typically over the internet. In contrast to a local attack, Mallory has no direct or physical access to Bob’s machine. Mallory instead uses poorly protected (or open) network ports or exploits vulnerabilities in the network-facing software or system configuration to gain unauthorized access to Bob’s machine.
On 27 June 2017, a new malware variant — eventually dubbed NotPetya by the internet security company Kaspersky who were first to discover the malware — started spreading in Ukraine, France, Germany, Italy, Poland, the United Kingdom, and the United States.
The hackers behind NotPetya initially compromised the software update mechanism of M.E.Doc, a tax software very popular among Ukrainian businesses, by inserting a backdoor. The backdoor remained dormant for at least 6 weeks prior to the attack. Forensic analysis of M.E.Doc’s servers revealed that software updates were not applied since 2013, uncovered hacker presence, and a compromised employee’s account on the update servers.
Leave a Reply