The malware subsequently started to quickly spread over networks by exploiting a security vulnerability in Windows operating systems called EternalBlue. EternalBlue, a security flaw in the Server Message Block (SMB) protocol used for sharing files over Windows networks, was originally discovered by the NSA. It allowed NotPetya to gain access to vulnerable Windows systems without user interaction. By exploiting EternalBlue, the malware was able to spread laterally across computer networks, infecting entire organizations in a very short period of time.
A.P. Moller Maersk A/S, the Copenhagen-based shipping company that transports about 20% of all global shipments, was among the approximately 600 companies hit by NotPetya. Maersk’s chief information security officer, Andrew Powell, gave a talk about the incident at Black Hat Europe 2019. According to his account, once a Maersk user was infected in the Odessa office, the malware spread so fast through the Maersk global network that most damage was done within seven minutes [139].
Once it infected a system, NotPetya encrypted files and overwrote the system’s Master Boot Record (MBR), thereby making the infected system completely unusable. Figure 19.6 shows the ransom note displayed by the malware on an infected system.
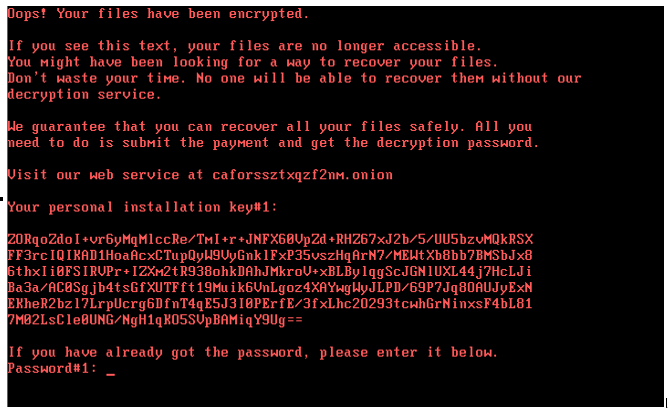
Figure 19.6: Ransom note displayed by NotPetya [156]
According to Powell, the malware destroyed 49,000 laptops, more than 1,000 applications, all file-sharing systems, the enterprise service bus, VMware vCenter cloud-management servers, and Maersk’s DHCP and Active Directory servers at Maersk. Even worse, because NotPetya was designed to also destroy online backups, Maersk’s primary and backup Active Directory systems were both irrecoverably damaged [139].
Due to good fortune, Maersk’s Lagos office had suffered a power outage while NotPetya was spreading through the company’s global network. As a result, Lagos’ IT systems, including the backup of Maersk’s Active Directory, were not damaged. Subsequently, the Lagos AD node was physically removed and flown to Copenhagen to rebuild the systems from scratch — a process that took over a week.
Andrew Powell has estimated that NotPetya caused damage, including the cost of recovery efforts, of about $300 million. This is close to the estimates for other large companies, such as the US pharmaceutical giant Merck and the logistics giant FedEx, where, according to the estimates, NotPetya incurred more than $300 million damage in lost business and recovery costs [139].
According to an article published by the Wired online magazine [77], the US White House assessed the total damage inflicted by NotPetya as more than $10 billion. That estimate was confirmed by the former Homeland Security advisor Tom Bassert, who was the most senior cybersecurity official in the US government at the time of the NotPetya attack.
Leave a Reply